Supported by world-class technology partners and industry leaders.
The modern internet was not built for authority at scale.
Each of these failures appears different, but they share the same root cause: authority is centralized, shareable, and fragile.
Every breach, account takeover, unauthorized API call, and compromised automation workflow is a symptom of this broken trust model.
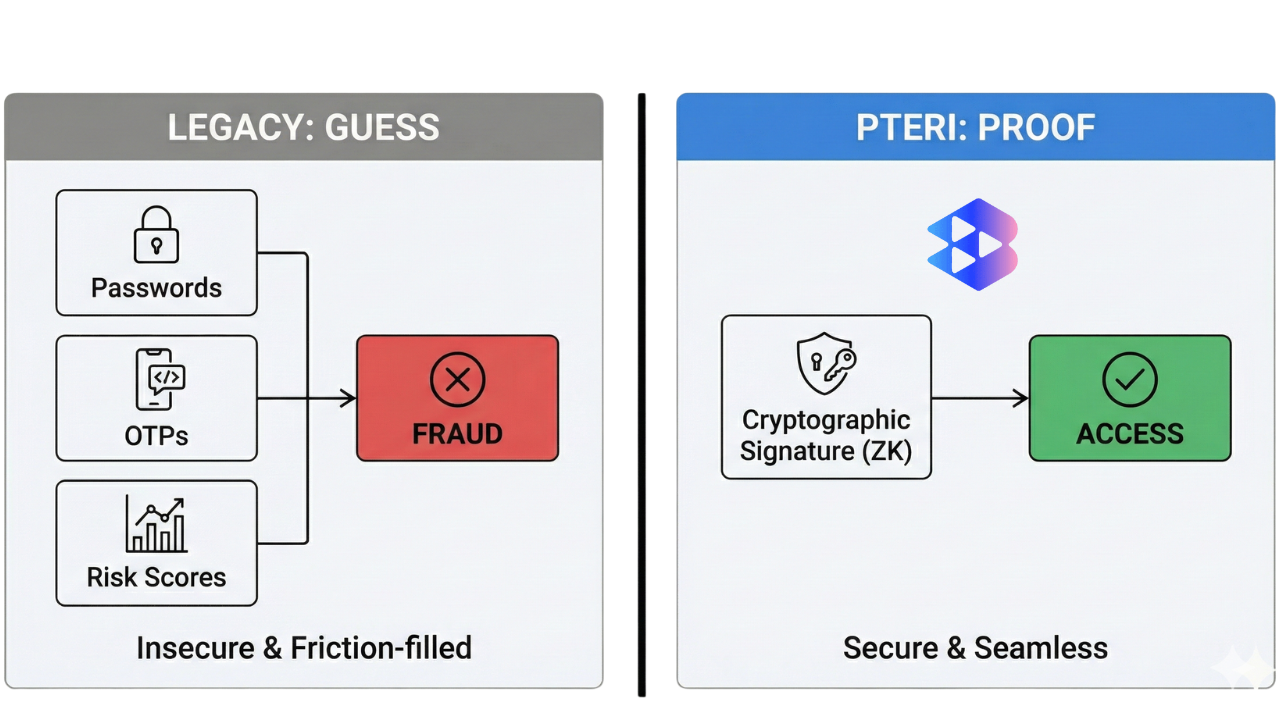
PTERI replaces this model entirely by making authority deterministic, self-custodial, and cryptographically verifiable at the moment of action.
AI systems act in the real world.
Kakr secures those actions with energy-backed cryptographic proof.
Most security systems rely on assumptions. Kakr replaces guessing with deterministic proof.
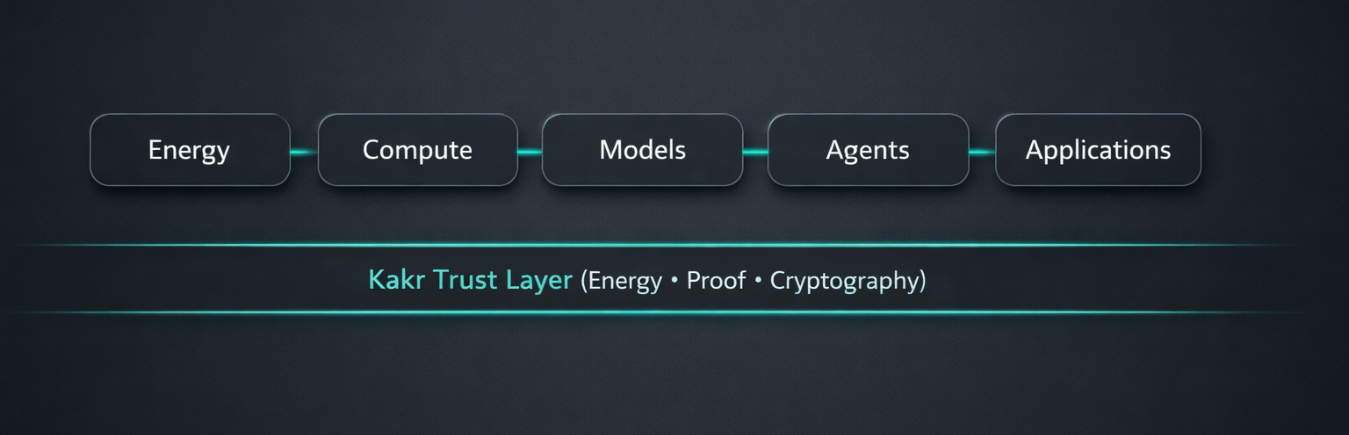
The Kakr platform provides a single trust layer across the entire AI stack.
Decentralized identity (DID) management for users and devices. Secure your ecosystem with self-sovereign identity principles, ensuring privacy and compliance by design.
Our team of engineers can help tailor the PTERI platform to your specific infrastructure needs.
Contact SalesAll Kakr components share the same cryptographic trust foundation.
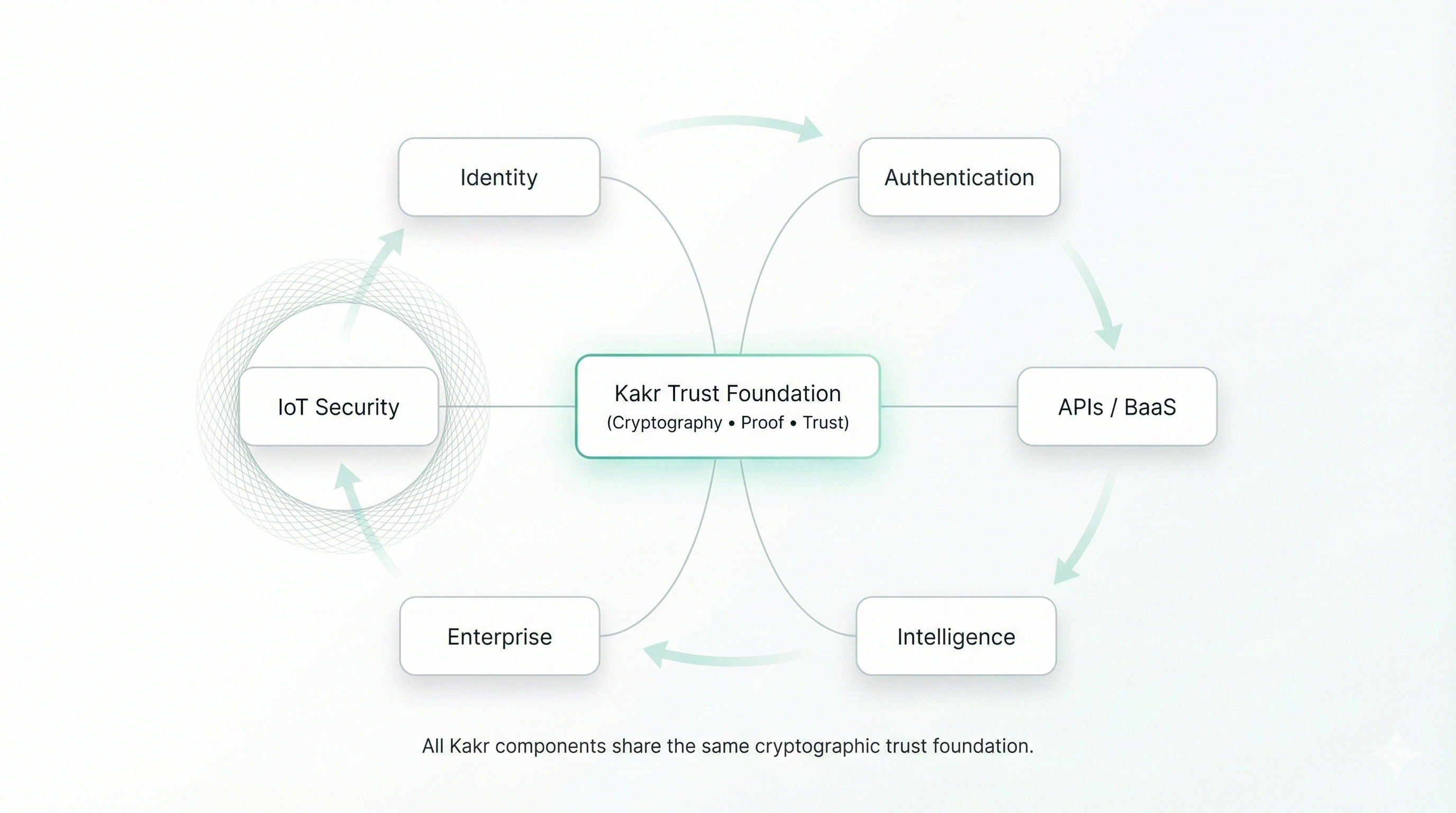
All PTERI capabilities - identity, payments, APIs, and AI delegation - operate on the same underlying authority model. Each surface is a different interface into the same carrier layer.
PTERI is not evaluated like a traditional authentication product or wallet.
It is a system-level replacement for shared secrets and custodial trust.
When evaluating PTERI, ask:
If the answer is yes, PTERI fits naturally into your stack.
Passwordless authentication for existing applications
Replacing OTP-based two-factor systems
Securing internal tools and admin access
Self-custodial payments and settlement
Controlled authority for AI agents and automation
We combine cutting-edge cryptography with robust infrastructure to deliver a platform that is secure, private, and scalable.
Only you hold the keys. No central honeypot. We ensure your assets remain truly yours through architecture that prioritizes sovereignty.
Prove attributes without exposing sensitive data. Leverage zero-knowledge proofs to validate identity with complete privacy.
Enterprise-grade scale and reliability. Built on infrastructure designed for 99.99% uptime and low-latency global performance.

Battle-tested security with privacy layers. Combining the immutable security of Proof of Work with MimbleWimble Extension Blocks.
Kakr replaces security categories - not just products.
Consolidating fragmented security into a single unified trust protocol.
Trusted by modern security teams
Watch how Liaas simplifies blockchain development
Moving from probabilistic security to deterministic proof.
(Litecoin)
Traditional Identity
Smart Contracts
Generic Infrastructure
A unified platform that connects devices, users, applications, and enterprises through decentralized identity, blockchain-backed authentication, and high-performance infrastructure.

Security Boundary: PTERI does not claim to protect compromised devices, user-approved malware, or physical coercion. Authority is enforced cryptographically, not behaviorally.